 Windows Security Log Event ID 4663
Windows Security Log Event ID 4663

4663: An attempt was made to access an object
On this page
This event is logged by multiple subcategories as indicated above.
This event documents actual operations performed against files and other objects. This event is logged between the open (4656) and close (4658) events for the object being opened and can be correlated to those events via Handle ID.
While event 4656 tells you when the object is initially opened and what type of access was requested at that time; 4656 doesn't give you positive confirmation any of the access permissions were actually exercised. That is the role of this event. This event, 4663, is logged the first time one or more of the requested permissions are actually exercised. If the program repeatedly exercises a permission while the object is open, Windows only logs 4663 the first time.
Note events 4656 and 4658 will not appear unless the subcategory "Handle Manipulation" is enabled along with the target sub-category. Microsoft explains that this was done to make it more difficult to enable these noisy events. They feel the event 4663 is better.
Win2012 adds Resource Attributes.
Free Security Log Resources by Randy
Subject:
The user and logon session that performed the action.
- Security ID: The SID of the account.
- Account Name: The account logon name.
- Account Domain: The domain or - in the case of local accounts - computer name.
- Logon ID is a semi-unique (unique between reboots) number that identifies the logon session. Logon ID allows you to correlate backwards to the logon event (4624) as well as with other events logged during the same logon session.
Object:
This is the object upon whom the action was attempted.
- Object Server: always "Security"
- Object Type: "File" for file or folder but can be other types of objects such as Key, SAM, SERVICE OBJECT, etc.
- Object Name: The name of the object being accessed
- Handle ID: is a semi-unique (unique between reboots) number that identifies all subsequent audited events while the object is open. Handle ID allows you to correlate to other events logged (Open 4656, Access 4663, Close 4658)
- Resource Attributes: (Win2012) Resource attributes a new feature that allows you to classify objects according to any number of things like project, compliance, security level. It's part of dynamic access control new to Win2012. See this webinar http://www.ultimatewindowssecurity.com/webinars/register.aspx?id=209 See the Win2012 example below. Also more information in this blog http://www.ultimatewindowssecurity.com/blog/default.aspx?p=5aea7883-80c4-40cb-b182-01240cc86070
Process Information:
- Process Name: Identifies the program executable that accessed the object.
- Process ID: The process ID specified when the executable started as logged in 4688.
Access Request Information:
- Accesses: These are permissions were actually exercised. The correspond to the permissions available in the Permission Entry dialog for any access control entry on the object.
- Access Mask: The bit-wise equivalent of Accesses.
Supercharger Enterprise
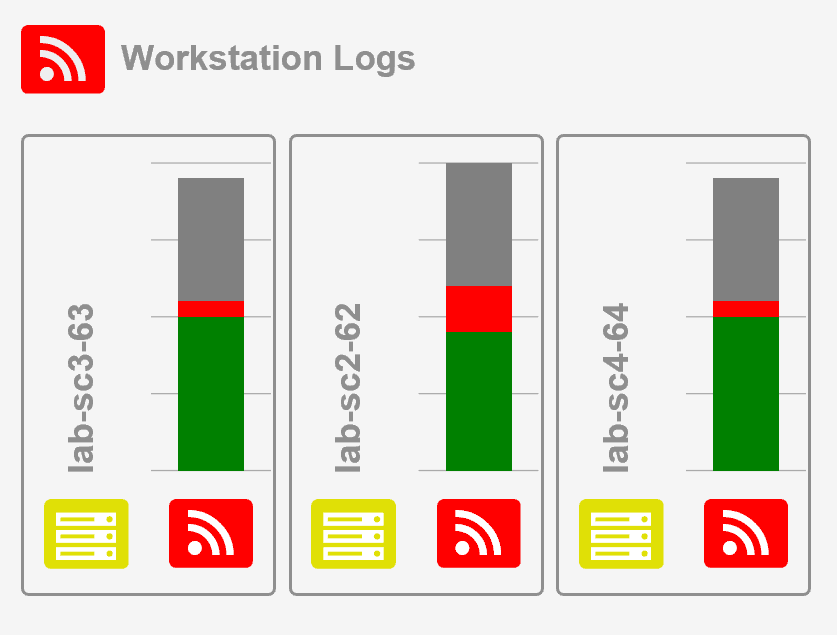
Load Balancing for Windows Event Collection
Win2008
File example:
An attempt was made to access an object.
Subject:
Security ID: ACME\Administrator
Account Name: Administrator
Account Domain: ACME
Logon ID: 0x1f41e
Object:
Object Server: Security
Object Type: File
Object Name: C:\sharedFiles\MasterEncryptionCode.txt
Handle ID: 0x40
Process Information:
Process ID: 0x1ac
Process Name: C:\Windows\System32\cmd.exe
Access Request Information:
Accesses: DELETE
Access Mask: 0x10000
Registry key example:
An attempt was made to access an object.
Subject:
Security ID: ACME\administrator
Account Name: administrator
Account Domain: ACME
Logon ID: 0x176293
Object:
Object Server: Security
Object Type: Key
Object Name: \REGISTRY\MACHINE\SOFTWARE\MTG
Handle ID: 0x124
Process Information:
Process ID: 0x8d4
Process Name: C:\Windows\regedit.exe
Access Request Information:
Accesses: Set key value
Access Mask: 0x2
Win2012
An attempt was made to access an object.
Subject:
Security ID: LB\administrator
Account Name: administrator
Account Domain: LB
Logon ID: 0x3DE02
Object:
Object Server: Security
Object Type: File
Object Name: C:\asdf\New Text Document.txt
Handle ID: 0x178
Resource Attributes: S:AI
Process Information:
Process ID: 0x113c
Process Name: C:\Windows\System32\notepad.exe
Access Request Information:
Accesses: WriteData (or AddFile)
AppendData (or AddSubdirectory or CreatePipeInstance)
Access Mask: 0x6
Top 10 Windows Security Events to Monitor
Free Tool for Windows Event Collection