 Windows Security Log Event ID 567
Windows Security Log Event ID 567

| Operating Systems |
Windows 2003 and XP
|
|
Category | Object Access |
|
Type
|
Success
Failure
|
Corresponding events
in Windows
2008
and Vista |
4657
,
4663
|
567: Object Access Attempt
On this page
Event 567 logs the actual permissions exercised by the user/program on the object after opening it. While event 560 logs the permissions the user/program obtained to the file or other object at the time it was opened, Event 567 asserts that the Accesses where actually used.
For this event to be useful - that is to identify the object accessed - you must find the preceding event 560 with the corresponding Handle ID.
While a user/program may repeatedly perform an operation on an open object, Windows only logs the first time a given permission is used. (I.E. a user may open a file and repeatedly save it while working on the file, but Windows will only log the first time WriteData permission was exercised to save the file)
See event ID 560 for additional information.
Free Security Log Resources by Randy
- Object Server:
- Handle ID:
- Object Type:
- Process ID:
- Image File Name:
- Accesses:
- Access Mask:
Supercharger Free Edition
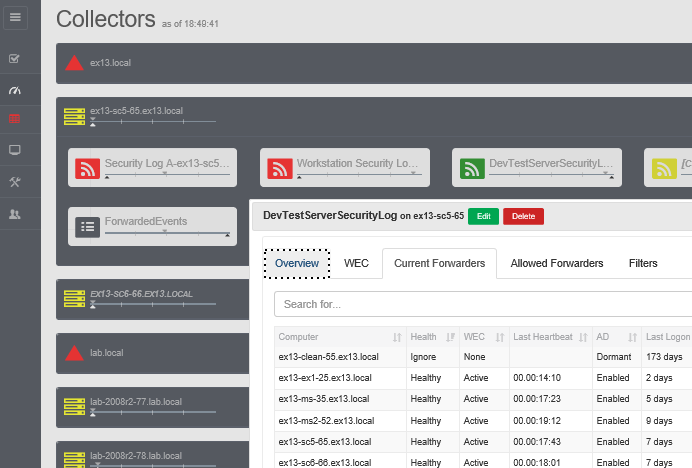
Your entire Windows Event Collection environment on a single pane of glass.
Free.