 Windows Security Log Event ID 4627
Windows Security Log Event ID 4627

| Operating Systems |
Windows 2016 and 10
Windows Server 2019 and 2022
Windows Server 2025
|
Category
• Subcategory | Logon/Logoff
• Group Membership |
|
Type
|
Success
|
Corresponding events
in Windows
2003
and before |
|
4627: Group membership information.
On this page
This is the only event of it's new Group Membership subcategory. One or more of these events are logged whenever a user logs on or a logon session begins for any other reason (see LogonTypes on 4624).
This event documents all the groups to which the user belongs.
This event is not really an event per se but a point-in-time documentation of the user's membership at the time of logon.
Free Security Log Resources by Randy
Subject:
Identifies the account that requested the logon - NOT the user who just logged on. Subject is usually Null or one of the Service principals and not usually useful information. See New Logon for who just logged on to the sytem.
- Security ID
- Account Name
- Account Domain
- Logon ID
Logon Type:
This is a valuable piece of information as it tells you HOW the user just logged on. See 4624
New Logon:
The user who just logged on is identified by the Account Name and Account Domain. You can determine whether the account is local or domain by comparing the Account Domain to the computer name. If they match, the account is a local account on that system, otherwise a domain account. See New Logon field description at 4624
- Security ID: the SID of the account
- Account Name: Logon name of the account
- Account Domain: Domain name of the account (pre-Win2k domain name)
- Logon ID: Semi-unique logon session ID number
Events in sequence:
If a user is member to too many groups to document in one event Windows will log multiple instances of this event.
Group Membership:
This is where all the groups are listed to whom the user belonged at time of logon.
This event has been tested with a domain account in a domain joined Windows 10 computer and we can confirm this event includes:
- the local groups on that computer to which the user belongs
- domain groups to which the user belongs
- all groups, including groups the user is a member of by virtue of nested group membership
- special principle SIDs the user has in their user token such as INTERACTIVE or NETWORK depending on type of logon. AKA Well Known SIDs
Supercharger Free Edition
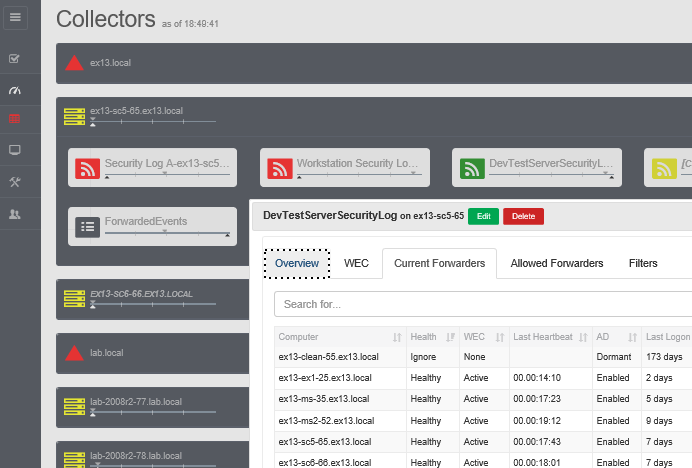
Your entire Windows Event Collection environment on a single pane of glass.
Free.
Group membership information.
Subject:
Security ID: AzureAD\RandyFranklinSmith
Account Name: RandyFranklinSmith
Account Domain: AzureAD
Logon ID: 0x7A202
Logon Type: 2
New Logon:
Security ID: DESKTOP-TMO9MI9\Administrator
Account Name: Administrator
Account Domain: DESKTOP-TMO9MI9
Logon ID: 0x1D80AF1
Event in sequence: 1 of 1
Group Membership:
DESKTOP-TMO9MI9\None
Everyone
NT AUTHORITY\Local account and member of Administrators group
BUILTIN\Administrators
BUILTIN\Users
NT AUTHORITY\INTERACTIVE
CONSOLE LOGON
NT AUTHORITY\Authenticated Users
NT AUTHORITY\This Organization
NT AUTHORITY\Authenticated Users3
LOCAL
NT AUTHORITY\NTLM Authentication
Mandatory Label\High Mandatory Level
Top 10 Windows Security Events to Monitor
Free Tool for Windows Event Collection