 Windows Security Log Event ID 4767
Windows Security Log Event ID 4767

| Operating Systems |
Windows 2008 R2 and 7
Windows 2012 R2 and 8.1
Windows 2016 and 10
Windows Server 2019 and 2022
|
Category
• Subcategory | Account Management
• User Account Management |
|
Type
|
Success
|
Corresponding events
in Windows
2003
and before |
671
|
4767: A user account was unlocked
On this page
The user identified by Subject: unlocked the user identified by Target Account:.
Note: this event is logged whenever you check the Unlock Account check box on the user's account tab - even if the account is not currently locked as a result of failed logon attempts. See event ID 4740.
This event is logged both for local SAM accounts and domain accounts.
Free Security Log Resources by Randy
Subject:
The user and logon session that performed the action.
- Security ID: The SID of the account.
- Account Name: The account logon name.
- Account Domain: The domain or - in the case of local accounts - computer name.
- Logon ID is a semi-unique (unique between reboots) number that identifies the logon session. Logon ID allows you to correlate backwards to the logon event (4624) as well as with other events logged during the same logon session.
Target Account:
- Security ID: SID of the account
- Account Name: name of the account
- Account Domain: domain of the account
Supercharger Enterprise
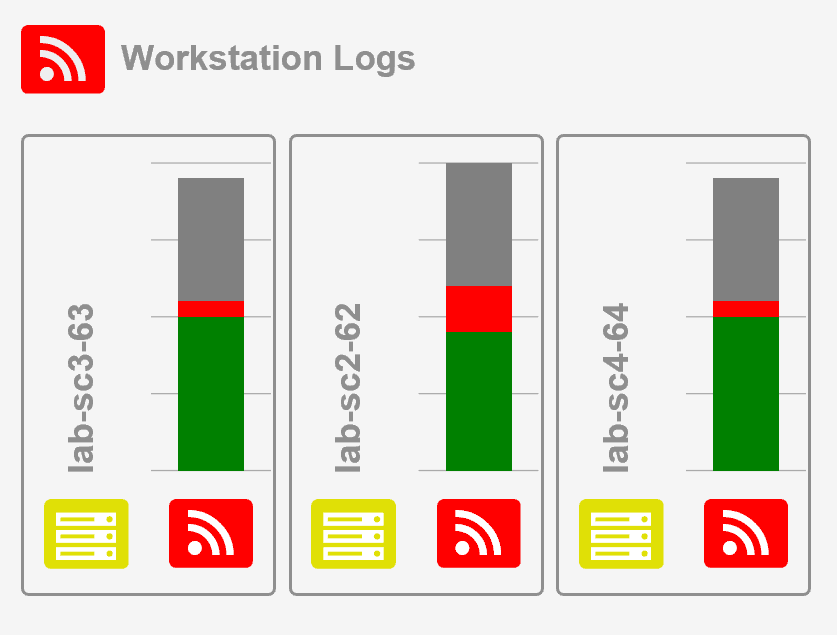
Load Balancing for Windows Event Collection