 Sysmon Event ID 20
Sysmon Event ID 20

20: WmiEventConsumer activity detected
This is an event from
Sysmon.
On this page
Attackers have developed a particularly sophisticated way to persist malware perhaps elevate privileges with WMI Event Filters and Consumers.
WMI allows you to link these 2 objects in order to execute a custom action whenever specified things happen in Windows. WMI events are related to but more general than the events we all know and love in the event log. WMI events include system startup, time intervals, program execution and many, many other things. You can define a __EventFilter which is basically a WQL query that specifies what events you want to catch in WMI. This is a permanent object saved in the WMI repository. It’s passive until you create a consumer and link them with a binding. The WMI event consumer defines what the system should do with any events caught by the filter. There are different kinds of event consumers for action like running a script, executing a command line, sending an email or writing to a log file. Finally, you link the filter and consumer with a __FilterToConsumerBinding. After saving the binding, everything is now active and whenever events matching the filter occur, they are fed to the consumer.
This event tells you when a WMI event consumer is registered documenting the consumer name, log, and destination. In an attack this is the 2nd of 3 setup steps. The consumer defines what gets executed when the an event is emitted by the filter (see Event ID 19). The 3rd step is recorded by Event ID 21.
To learn more about this kind of attack see my blog https://www.ultimatewindowssecurity.com/blog/default.aspx?d=06/2018
Free Security Log Resources by Randy
- Log Name
- Source
- Date
- Event ID
- Task Category
- Level
- Keywords
- User
- Computer
- Description
- EventType
- UtcTime
- Operation
- User
- Name
- Type
- Destination
Supercharger Enterprise
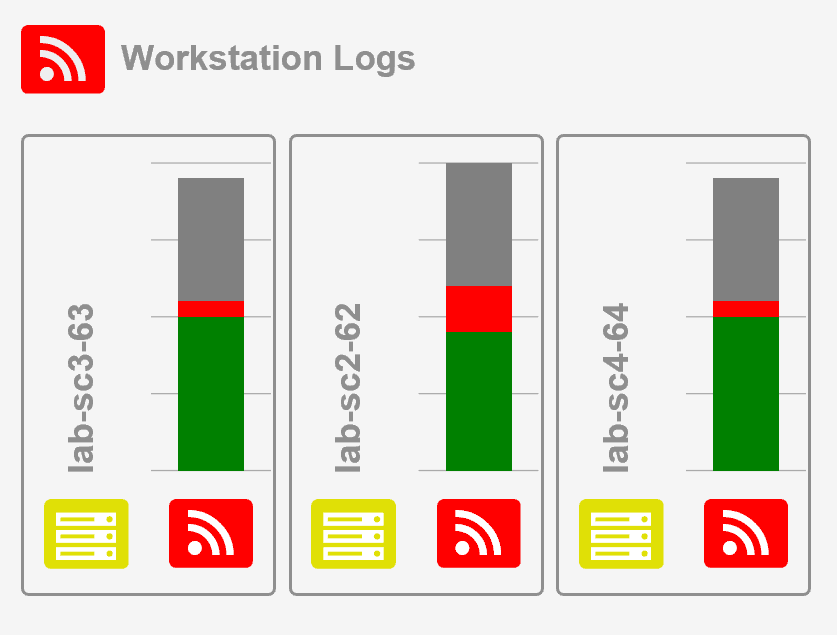
Load Balancing for Windows Event Collection
Log Name: Microsoft-Windows-Sysmon/Operational
Source: Microsoft-Windows-Sysmon
Date: 4/11/2018 9:26:16 AM
Event ID: 20
Task Category: WmiEventConsumer activity detected (rule: WmiEvent)
Level: Information
Keywords:
User: SYSTEM
Computer: rfsh.lab.local
Description:
WmiEventConsumer activity detected:
EventType: WmiConsumerEvent
UtcTime: 2018-04-11 16:26:16.360
Operation: Created
User: LAB\rsmith
Name: "BotConsumer23"
Type: Command Line
Destination: "C:\\Windows\\System32\\evil.exe"
Event Xml:
<Event xmlns="http://schemas.microsoft.com/win/2004/08/events/event">
<System>
<Provider Name="Microsoft-Windows-Sysmon" Guid="{5770385F-C22A-43E0-BF4C-06F5698FFBD9}" />
<EventID>20</EventID>
<Version>3</Version>
<Level>4</Level>
<Task>20</Task>
<Opcode>0</Opcode>
<Keywords>0x8000000000000000</Keywords>
<TimeCreated SystemTime="2018-04-11T16:26:16.360473200Z" />
<EventRecordID>63557</EventRecordID>
<Correlation />
<Execution ProcessID="7620" ThreadID="21880" />
<Channel>Microsoft-Windows-Sysmon/Operational</Channel>
<Computer>rfsh.lab.local</Computer>
<Security UserID="S-1-5-18" />
</System>
<EventData>
<Data Name="EventType">WmiConsumerEvent</Data>
<Data Name="UtcTime">2018-04-11 16:26:16.360</Data>
<Data Name="Operation">Created</Data>
<Data Name="User">LAB\rsmith</Data>
<Data Name="Name"> "BotConsumer23"</Data>
<Data Name="Type">Command Line</Data>
<Data Name="Destination"> "C:\\Windows\\System32\\evil.exe"</Data>
</EventData>
</Event>
Top 10 Windows Security Events to Monitor
Free Tool for Windows Event Collection