 Windows Security Log Event ID 626
Windows Security Log Event ID 626

| Operating Systems |
Windows Server 2000
Windows 2003 and XP
|
|
Category | Account Management |
|
Type
|
Success
|
Corresponding events
in Windows
2008
and Vista |
4722
|
626: User Account Enabled
On this page
Despite MS documentation, this event does not get logged by W2k but W3 does log this event correctly. However W2k does log event 642 and identifies the type of change. See example below: W3 also logs 642 along with this event but the format of 642 is different compared to W2k. See 642 for W3.
Event ID:642
Description:
User Account Changed:
Account Enabled.
Target Account Name:user
Target Domain:ELMW2
Target Account ID:ELMW2\user
Caller User Name:Administrator
Caller Domain:ELMW2
Caller Logon ID:(0x0,0x12D622)
Privileges:-Note Windows 2000 does not log event ID 626 explicitly. Results are logged as a part of event ID 642 in the description of the message. Windows Server 2003 DOES logs this event. This event will be accompanied by an event 642.
Free Security Log Resources by Randy
- Target Account Name: %1
- Target Domain: %2
- Target Account ID: %3
- Caller User Name: %4
- Caller Domain: %5
- Caller Logon ID: %6
Supercharger Enterprise
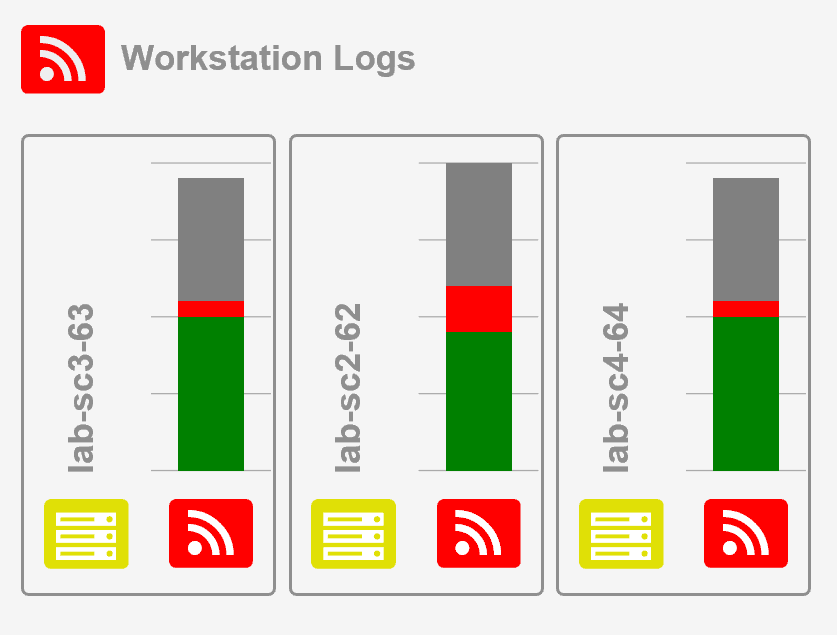
Load Balancing for Windows Event Collection