 Windows Security Log Event ID 552
Windows Security Log Event ID 552

| Operating Systems |
Windows 2003 and XP
|
|
Category | Logon/Logoff |
|
Type
|
Success
|
Corresponding events
in Windows
2008
and Vista |
4648
|
552: Logon attempt using explicit credentials
On this page
Event 552 is logged when a process logs on as a different account such as when the Scheduled Tasks service starts a task as the specified user. Logged on user: specifies the original user account.
User whose credentials were used: specifies the new user account. Caller process ID: the process that performed this action. Look for a prior event 592 with the same process id. Target Server Name and Info have always been observed as "local host" and source network address and port as empty.
Free Security Log Resources by Randy
- Logged on user:
- User Name:
- Domain:
- Logon ID:
- Logon GUID:
- User whose credentials were used:
- Target User Name:
- Target Domain: MTG
- Target Logon GUID:
- Target Server Name:
- Target Server Info:
- Caller Process ID:
- Source Network Address:
- Source Port:
Supercharger Free Edition
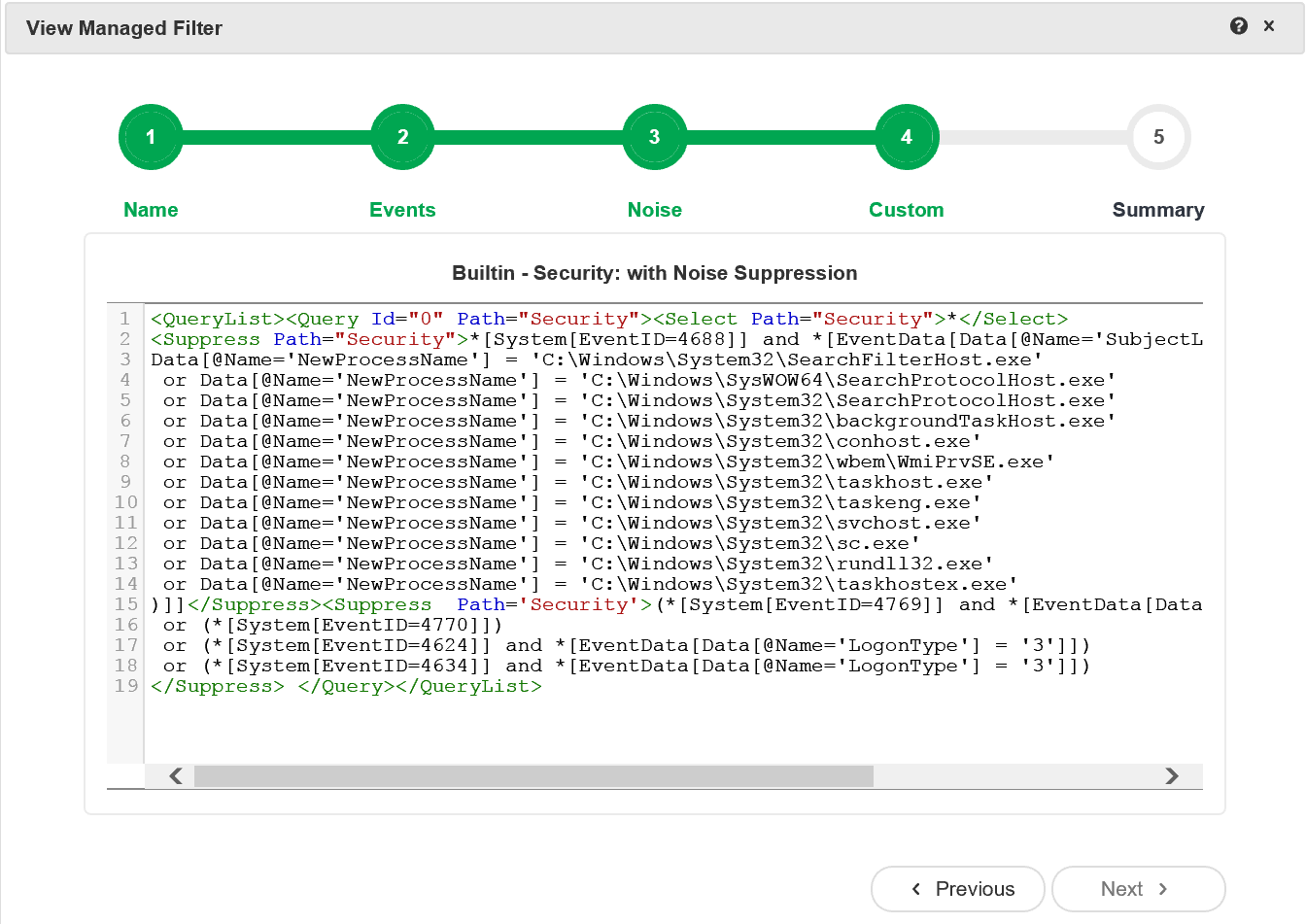
Supercharger's built-in Xpath filters leave the noise behind.
Free.
Logon attempt using explicit credentials:
Logged on user:
User Name: MTG1$
Domain: MTG
Logon ID: (0x0,0x3E7)
Logon GUID: -
User whose credentials were used:
Target User Name: bozo
Target Domain: MTG
Target Logon GUID: {8e3681a4-23bd-54ef-89bb-20b3b12e3512}
Target Server Name: localhost
Target Server Info: localhost
Caller Process ID: 960
Source Network Address: -
Source Port: -
Top 10 Windows Security Events to Monitor
Free Tool for Windows Event Collection