Chapter 10
Privilege Use Events
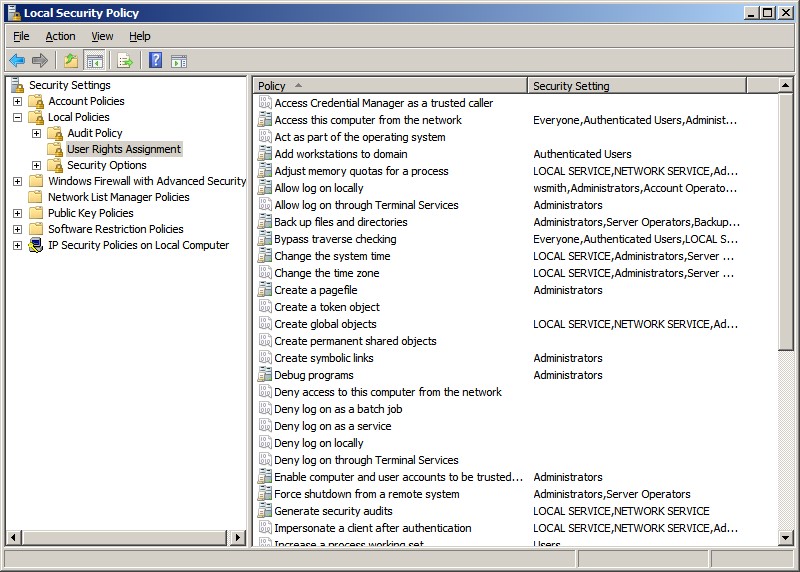
You can use the Privilege Use audit category to track the
exercise of user rights. Microsoft uses the terms privilege, right, and permission inconsistently. In the case of this audit
category, privilege refers to most
of the user rights that you find in the Local Security Policy under Security
Settings\Local Policies\User Rights Assignment — with one important
exception. Intermingled within those user rights are logon rights. Logon rights
such as Allow logon locally and Access this computer from the network are not addressed by the Privilege Use category because they aren’t technically user rights. (To find out when a logon right is exercised, you can refer to the Logon/Logoff category’s Logon subcategory, which we discussed in Chapter 5).
The chart below lists the subcategories of the Privilege Use
category, along with the privileges that Microsoft considers Sensitive
Privilege Use and Non Sensitive Privilege Use. We have not observed any events
in the Non Sensitive Privilege Use subcategory, and most of the listed
privileges in this category are not audited.
|
Privilege Use Subcategories
|
Included Privileges
|
|
Sensitive Privilege Use
|
Act as part of the operating system
Back up files and directories
Create a token object
Debug programs
Enable computer and user accounts to be trusted for delegation
Generate security audits
Impersonate a client after authentication
Load and unload device drivers
Manage auditing and security log
Modify firmware environment values
Replace a process-level token
Restore files and directories
Take ownership of files or other objects
|
|
Non Sensitive Privilege Use
|
Access Credential Manager as a trusted caller
Access this computer from the network
Add workstations to domain
Adjust memory quotas for a process
Allow logon locally
Allow logon through Terminal Services
Bypass traverse checking
Change the system time
Create a pagefile
Create global objects
Create permanent shared objects
Create symbolic links
Deny access this computer from the network
Deny log on as a batch job
Deny log on as a service
Deny log on locally
Deny log on through Terminal Services
Force shutdown from a remote system
Increase a process working set
Increase scheduling priority
Lock pages in memory
Log on as a batch job
Log on as a service
Modify an object label
Perform volume maintenance tasks
Profile single process
Profile system performance
Remove computer from docking station
Shut down the system
Synchronize directory service data
|
|
Other Privilege Use Events
|
No events in this subcategory
|
The Privilege Use category logs two events.
|
Event ID
|
Title
|
|
4673
|
A privileged service was called
|
|
4674
|
An operation was attempted on a privileged object
|
For most user rights, Windows logs a Privilege Use event
when a user exercises the right. However, some rights are exercised so
frequently during the normal course of a user’s activities that the Security
log would quickly fill if Windows were to log each use. Therefore Windows
doesn’t normally log some rights. Among these high-use rights are Back up
files and directories and Restore files and directories.
You can force Windows to log these two rights
by enabling the Audit: Audit the use of Backup and Restore privilegesecurity option, but enabling this option will
result in a Privilege Use event being logged for every single file, folder, and
other object during system backups, overwhelming your log with events of
questionable value.
Backup and Restore privileges are also used at other
times, specifically whenever an application attempts access through the NTFS
backup API. For normal user rights, Windows logs either event ID
4673 or event ID 4674 when right is exercised. As mentioned earlier, logon
rights are never logged by Privilege Use events: The use of logon rights is
documented by Logon/Logoff events. Event ID 4674 has to do with a privilege
that is used to access an object. Therefore, this event lists the object name.
Event ID 4673 lists the affected process and service name.
|
System Name of Privilege
|
Description
|
Notes
|
|
SeTcbPrivilege
|
Act as part of the operating system
|
Logged frequently Event 4673
|
|
SeMachineAccountPrivilege
|
Add workstations to domain
|
Not logged
|
|
SeBackupPrivilege
|
Back up files and directories
|
Logged only when the
Audit the use of Backup and
Restore privilege
security option is enabled
|
|
SeCreatePermanentPrivilege
|
Create permanent shared objects
|
|
|
SeEnableDelegationPrivilege
|
Enable computer and user accounts to be trusted for
delegation
|
|
|
SeRemoteShutdownPrivilege
|
Force shutdown from a remote system
|
|
|
SeLoadDriverPrivilege
|
Load and unload device drivers
|
|
|
SeRestorePrivilege
|
Restore files and directories
|
Logged only when the
Audit the use of Backup and
Restore privilege
security option is enabled
|
|
SeSecurityPrivilege
|
Manage auditing and Security log
|
Event 4674
|
|
SeShutdownPrivilege
|
Shut down the system
|
Event 4674
|
|
SeTakeOwnershipPrivilege
|
Take ownership of files or other objects
|
Event 4674
|
|
SeIncreaseBasePriorityPrivilege
|
Increase Scheduling Priority
|
Event 4673
|
By default, the following rights are suppressed and not
audited by the Privilege Use category:
- ChangeNotifyPrivilege
- AuditPrivilege
- CreateTokenPrivilege
- AssignPrimaryTokenPrivilege
- BackupPrivilege
- RestorePrivilege
- DebugPrivilege
Bottom Line
The Privilege Use category generates a lot of noise, and we
usually recommend leaving it disabled. In fact, Microsoft’s former Security log
guru,
Eric Fitzgerald, as much as says that this audit policy and its events are
useless because no “central reference” of which operations are controlled by
each privilege exists. That lack reduces the value of this category.