 Sysmon Event ID 3
Sysmon Event ID 3

3: Network connection detected
This is an event from
Sysmon.
On this page
The network connection event logs TCP/UDP connections on the machine. It is disabled by default. Each connection is linked to a process through the ProcessId and ProcessGUID fields. The event also contains the source and destination host names IP addresses, port numbers and IPv6 status.
Free Security Log Resources by Randy
- Log Name
- Source
- Loggged
- Event ID
- Task Category
- Level
- Keywords
- User
- Computer
- OpCode
- Description
- RuleName
- UtcTime
- ProcessGuid
- ProcessId
- Image
- User
- Protocol
- Initiated
- SourceIsIpv6
- SourceIp
- SourceHostname
- SourcePort
- SourcePortName
- DestinationIsIpv6
- DestinationIp
- DestinationHostname
- DestinationPort
- DestinationPortName
Supercharger Free Edition
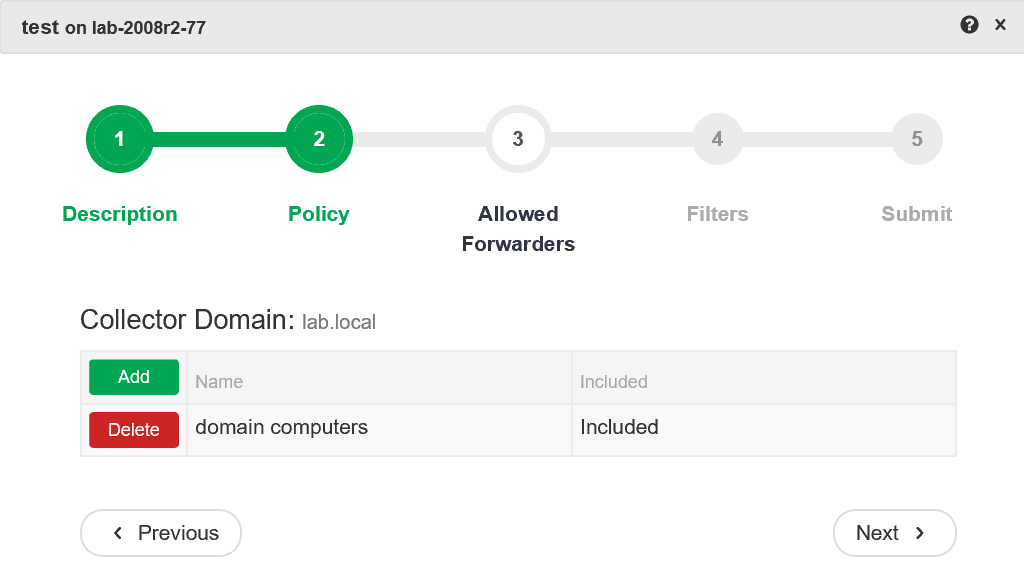
Centrally manage WEC subscriptions.
Free.
Network connection detected
RuleName: RDP
UtcTime: 2017-04-28 22:12:22.557
ProcessGuid: {a23eae89-bd28-5903-0000-00102f345d00}
ProcessId: 13220
Image: C:\Program Files (x86)\Google\Chrome\Application\chrome.exe
User: LAB\rsmith
Protocol: tcp
Initiated: true
SourceIsIpv6: false
SourceIp: 192.168.1.250
SourceHostname: rfsH.lab.local
SourcePort: 3328
SourcePortName:
DestinationIsIpv6: false
DestinationIp: 104.130.229.150
DestinationHostname:
DestinationPort: 3389
DestinationPortName: ms-wbt-server
Event XML:
<Event xmlns="http://schemas.microsoft.com/win/2004/08/events/event">
<System>
<Provider Name="Microsoft-Windows-Sysmon" Guid="{5770385F-C22A-43E0-BF4C-06F5698FFBD9}" />
<EventID>3</EventID>
<Version>5</Version>
<Level>4</Level>
<Task>3</Task>
<Opcode>0</Opcode>
<Keywords>0x8000000000000000</Keywords>
<TimeCreated SystemTime="2017-04-28T22:12:23.657698300Z" />
<EventRecordID>10953</EventRecordID>
<Correlation />
<Execution ProcessID="3216" ThreadID="3976" />
<Channel>Microsoft-Windows-Sysmon/Operational</Channel>
<Computer>rfsH.lab.local</Computer>
<Security UserID="S-1-5-18" />
</System>
<EventData>
<Data Name="RuleName">RDP</Data>
<Data Name="UtcTime">2017-04-28 22:12:22.557</Data>
<Data Name="ProcessGuid">{A23EAE89-BD28-5903-0000-00102F345D00}</Data>
<Data Name="ProcessId">13220</Data>
<Data Name="Image">C:\Program Files (x86)\Google\Chrome\Application\chrome.exe</Data>
<Data Name="User">LAB\rsmith</Data>
<Data Name="Protocol">tcp</Data>
<Data Name="Initiated">true</Data>
<Data Name="SourceIsIpv6">false</Data>
<Data Name="SourceIp">192.168.1.250</Data>
<Data Name="SourceHostname">rfsH.lab.local</Data>
<Data Name="SourcePort">3328</Data>
<Data Name="SourcePortName">-</Data>
<Data Name="DestinationIsIpv6">false</Data>
<Data Name="DestinationIp">104.130.229.150</Data>
<Data Name="DestinationHostname">lab-sc-100</Data>
<Data Name="DestinationPort">3389</Data>
<Data Name="DestinationPortName">ms-wbt-server</Data>
</EventData>
</Event>
Top 10 Windows Security Events to Monitor
Free Tool for Windows Event Collection