 Windows Security Log Event ID 4794
Windows Security Log Event ID 4794

| Operating Systems |
Windows 2008 R2 and 7
Windows 2012 R2 and 8.1
Windows 2016 and 10
Windows Server 2019 and 2022
|
Category
• Subcategory | Account Management
• User Account Management |
|
Type
|
Success
|
Corresponding events
in Windows
2003
and before |
|
4794: An attempt was made to set the Directory Services Restore Mode administrator password
On this page
This event is logged whenever you successfully set the DSRM administrator password such as with ntdsutil.
This password is important since it controls someone's ability to enter DSRM and potentially restore or other wise access the Active Directory database.
Free Security Log Resources by Randy
Subject:
The user and logon session that performed the action.
- Security ID: The SID of the account.
- Account Name: The account logon name.
- Account Domain: The domain or - in the case of local accounts - computer name.
- Logon ID is a semi-unique (unique between reboots) number that identifies the logon session. Logon ID allows you to correlate backwards to the logon event (4624) as well as with other events logged during the same logon session.
Additional Information:
- Caller Workstation: computer name where the user was present; only relevant if user made the change remotely
- Status Code: Always "0x0"? Start a discussion if you have information on this field!
Supercharger Free Edition
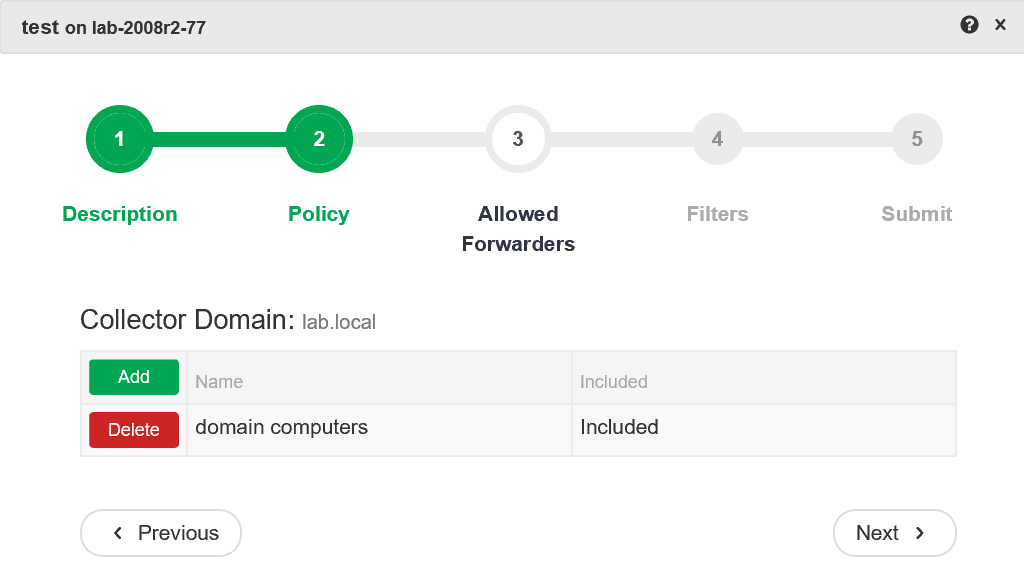
Centrally manage WEC subscriptions.
Free.