 Windows Security Log Event ID 4672
Windows Security Log Event ID 4672

| Operating Systems |
Windows 2008 R2 and 7
Windows 2012 R2 and 8.1
Windows 2016 and 10
Windows Server 2019 and 2022
Windows Server 2025
|
Category
• Subcategory | Logon/Logoff
• Special Logon |
|
Type
|
Success
|
Corresponding events
in Windows
2003
and before |
576
|
4672: Special privileges assigned to new logon
On this page
This event lets you know whenever an account assigned any "administrator equivalent" user rights logs on. For instance you will see event 4672 in close proximity to logon events (4624) for administrators since administrators have most of these admin-equivalent rights.
So, this is a useful right to detecting any "super user" account logons. Of course this right is logged for any server or applications accounts logging on as a batch job (scheduled task) or system service. See Logon Type: on event ID 4624. You can correlate 4672 to 4624 by Logon ID:.
Note: "User rights" and "privileges" are synonymous terms used interchangeably in Windows.
Admin-equivalent rights are powerful authorities that allow you to circumvent other security controls in Windows. Most admin equivalent privileges are intended for services and applications that interact closely with the operating system. With just a few exceptions, most admin equivalent privileges neither need nor should be granted to human user accounts.
Some Microsoft documentation puts this in the "Sensitive Privilege Use / Non-Sensitive Privilege Use" subcategory. However our testing finds this in the "Special Logon" Category.
Free Security Log Resources by Randy
Subject:
The ID and logon session of the administrator-equivalent user that just logged on.
- Security ID: The SID of the account.
- Account Name: The account logon name.
- Account Domain: The domain or - in the case of local accounts - computer name.
- Logon ID is a semi-unique (unique between reboots) number that identifies the logon session. Logon ID allows you to correlate backwards to the logon event (4624) as well as with other events logged during the same logon session.
Privileges:
The names of all the admin-equivalent privileges the user held at the time of logon.
Supercharger Enterprise
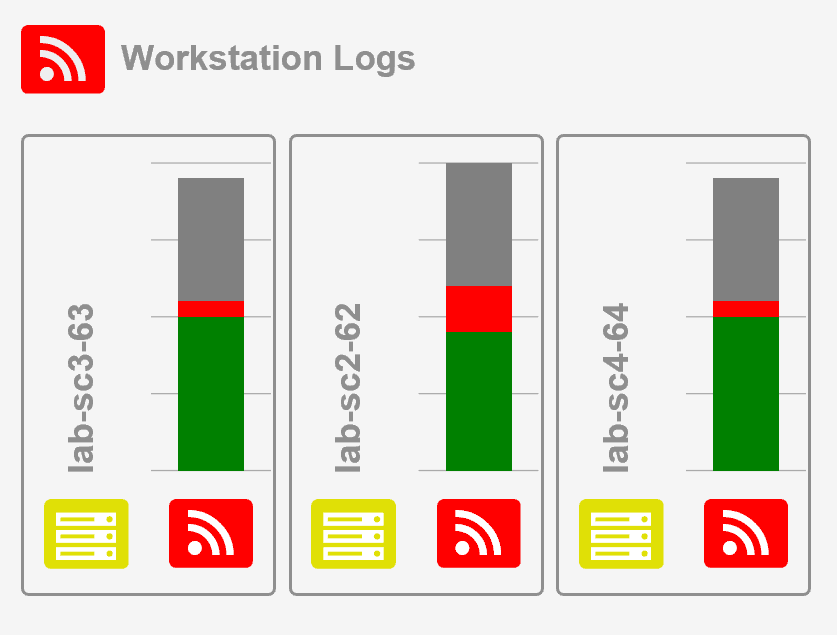
Load Balancing for Windows Event Collection
Special privileges assigned to new logon.
Subject:
Security ID: WIN-R9H529RIO4Y\Administrator
Account Name: Administrator
Account Domain: WIN-R9H529RIO4Y
Logon ID: 0x4b842
Privileges:
SeSecurityPrivilege
SeTakeOwnershipPrivilege
SeLoadDriverPrivilege
SeBackupPrivilege
SeRestorePrivilege
SeDebugPrivilege
SeSystemEnvironmentPrivilege
SeImpersonatePrivilege
Top 10 Windows Security Events to Monitor
Free Tool for Windows Event Collection