 Sysmon Event ID 18
Sysmon Event ID 18

18: Pipe connected
This is an event from
Sysmon.
On this page
Named pipes are an inteprocess communication (IPC) method in Windows similar to Sockets/TCP. Named pipes are possible to be used over the network but very uncommon given today's ubiquity of IP networks. Name pipes are still used extensively for IPC between proceses on the same Windows system - including by malware components. With this event Sysmon allows you to monitor the creation of named pipes which could be useful for detecting malware after footprint any harmless pipes created by legitimate programs. SQL Server named pipes for instance are often used by local client processes.
This event shows the connection to a named pipe by a client process. Event ID 17 documents any connections to the pipe by a client.
Free Security Log Resources by Randy
- Log Name
- Source
- Date
- Event ID
- Task Category
- Level
- Keywords
- User
- Computer
- Description
- Pipe Connected
- UtcTime
- ProcessGuid
- ProcessId
- PipeName
- Image
Supercharger Free Edition
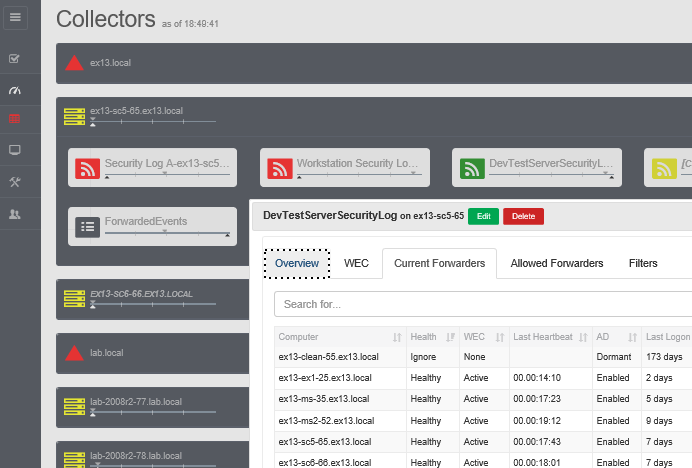
Your entire Windows Event Collection environment on a single pane of glass.
Free.
Log Name: Microsoft-Windows-Sysmon/Operational
Source: Microsoft-Windows-Sysmon
Date: 4/11/2018 9:07:50 AM
Event ID: 18
Task Category: Pipe Connected (rule: PipeEvent)
Level: Information
Keywords:
User: SYSTEM
Computer: rfsh.lab.local
Description:
Pipe Connected:
UtcTime: 2018-04-11 16:07:50.880
ProcessGuid: {c47a3e70-1e13-5ace-0000-001004ab2d00}
ProcessId: 2384
PipeName: \wkssvc
Image: C:\WINDOWS\Explorer.EXE
Event Xml:
<Event xmlns="http://schemas.microsoft.com/win/2004/08/events/event">
<System>
<Provider Name="Microsoft-Windows-Sysmon" Guid="{5770385F-C22A-43E0-BF4C-06F5698FFBD9}" />
<EventID>18</EventID>
<Version>1</Version>
<Level>4</Level>
<Task>18</Task>
<Opcode>0</Opcode>
<Keywords>0x8000000000000000</Keywords>
<TimeCreated SystemTime="2018-04-11T16:07:50.881699300Z" />
<EventRecordID>59778</EventRecordID>
<Correlation />
<Execution ProcessID="7620" ThreadID="21808" />
<Channel>Microsoft-Windows-Sysmon/Operational</Channel>
<Computer>rfsh.lab.local</Computer>
<Security UserID="S-1-5-18" />
</System>
<EventData>
<Data Name="UtcTime">2018-04-11 16:07:50.880</Data>
<Data Name="ProcessGuid">{C47A3E70-1E13-5ACE-0000-001004AB2D00}</Data>
<Data Name="ProcessId">2384</Data>
<Data Name="PipeName">\wkssvc</Data>
<Data Name="Image">C:\WINDOWS\Explorer.EXE</Data>
</EventData>
</Event>
Top 10 Windows Security Events to Monitor
Free Tool for Windows Event Collection