 Windows Security Log Event ID 848
Windows Security Log Event ID 848

| Operating Systems |
Windows 2003 and XP
|
|
Category | Policy Change |
|
Type
|
Success
|
Corresponding events
in Windows
2008
and Vista |
4944
|
848: The following policy was active when the Windows Firewall started
On this page
This event is logged once each time Windows Firewall start which is usually at boot up. This event documents the highlevel policy settings in effect at the time of startup.
Free Security Log Resources by Randy
- Group Policy Applied: should indicate whether Windows Firewall was getting its settings from Group Policy or the system's local policy but this appears to always say "No"
- Profile Used: "Standard" or "Domain". Windows Firewall seems to always start in Public and then switch to Domain shortly after if appropriate.
- Interfaces: which NICs? "All interfaces", if all.
- Operational mode: Whether Windows Firewall was enabled or not. Should usually say "On".
Services
- File and Printer Sharing: Disabled/Enabled
- Remote Desktop: Disabled/Enabled
- UPnP Framework: Disabled/Enbabled
- Allow Remote Administration: Disabled/Enbabled
- Allow Unicast Responses to Multicast/Broadcast Traffic: Enabled/Disabled
Security Logging:
The logging referred to here has nothing to do with the Security event log; instead it's referring to the C:\Windows\system32\LogFiles\Firewall\pfirewall.log log.
These fields corresponds to the check box in the Customize Loggin Settings for the Public/Domain Profile dialog in Windows Firewall with Advanced Security MMC console.
- Log dropped packets: Disabled/Enabled/-
- Log successful connections: Disabled/Enabled/-
ICMP:
- Allow incoming echo request: Disabled/Enabled/-
- Allow incoming timestamp request: Disabled/Enabled/-
- Allow incoming mask request: Disabled/Enabled/-
- Allow incoming router request: Disabled/Enabled/-
- Allow outgoing destination unreachable: Disabled/Enabled/-
- Allow outgoing source quench: Disabled/Enabled/-
- Allow outgoing parameter problem: Disabled/Enabled/-
- Allow outgoing time exceeded: Disabled/Enabled/-
- Allow redirect: Disabled/Enabled/-
- Allow outgoing packet too big: Disabled/Enabled/-
Supercharger Free Edition
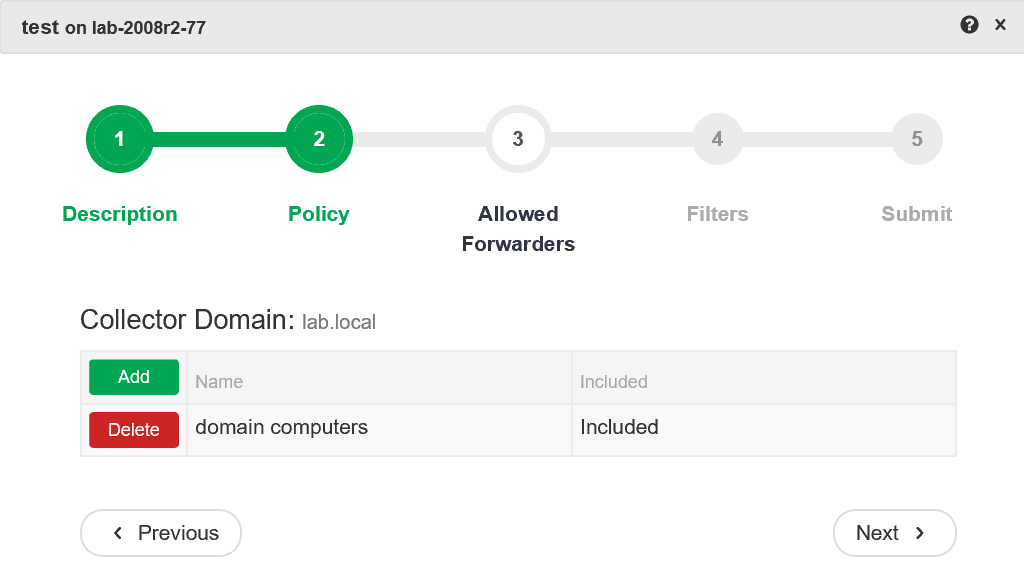
Centrally manage WEC subscriptions.
Free.
The following policy was active when the Windows Firewall started.
Group Policy applied: No
Profile used: Standard
Interface: All interfaces
Operational mode: On
Services:
File and Printer Sharing: Disabled
Remote Desktop: Enabled
UPnP Framework: Disabled
Allow remote administration: Disabled
Allow unicast responses to multicast/broadcast traffic: Disabled
Security Logging:
Log dropped packets: Disabled
Log successful connections: Disabled
ICMP:
Allow incoming echo request: Enabled
Allow incoming timestamp request: Disabled
Allow incoming mask request: Disabled
Allow incoming router request: Disabled
Allow outgoing destination unreachable: Disabled
Allow outgoing source quench: Disabled
Allow outgoing parameter problem: Disabled
Allow outgoing time exceeded: Disabled
Allow redirect: Disabled
Allow outgoing packet too big: Disabled
Top 10 Windows Security Events to Monitor
Free Tool for Windows Event Collection