 Windows Security Log Event ID 539
Windows Security Log Event ID 539

| Operating Systems |
Windows Server 2000
Windows 2003 and XP
|
|
Category | Logon/Logoff |
|
Type
|
Failure
|
Corresponding events
in Windows
2008
and Vista |
4625
|
539: Logon Failure - Account locked out
On this page
Do not confuse this with event 644.
This event is logged on the workstation or server where the user failed to logon. To determine if the user was present at this computer or elsewhere on the network, see event 528 for a list of logon types
This event is only logged on domain controllers when a user fails to logon to the DC itself such at the console or through failure to connect to a shared folder. On workstations and servers this event could be generated by a an attempt to logon with a domain or local SAM account. If a local SAM account, there will be a corresponding failure event from the Account Logon category.
Logon Type: See event 528.
To identify the source of network logon failures check the Workstation Name and Source Network Address fields.
Logon Process and Authentication Package will vary according to the type of logon and authentication protocol used.
Free Security Log Resources by Randy
- User Name:
- Domain:
- Logon Type:
- Logon Process:
- Authentication Package:
- Workstation Name:
The following fields are added in Windows Server 2003:
- Caller User Name:
- Caller Domain:
- Caller Logon ID:
- Caller Process ID:
- Transited Services:
- Source Network Address:
- Source Port:
Supercharger Enterprise
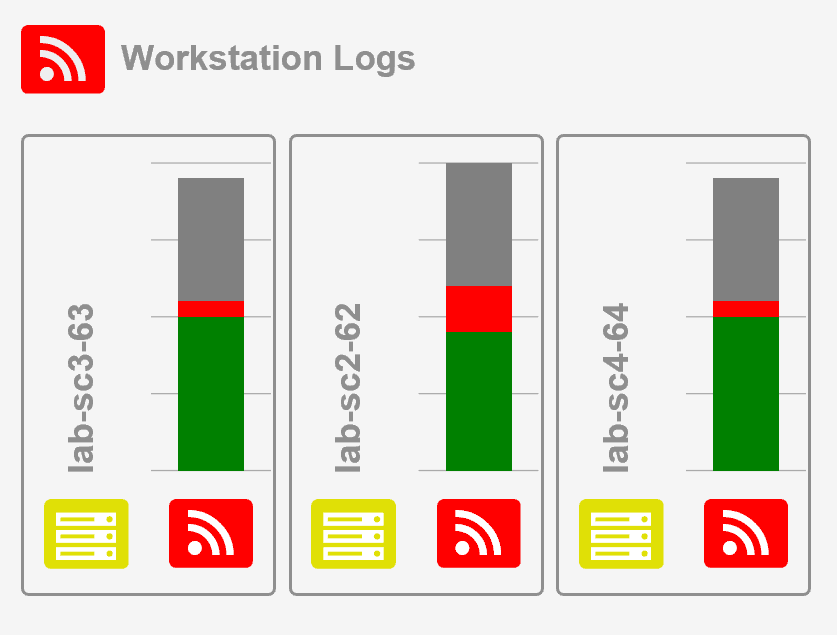
Load Balancing for Windows Event Collection
Logon Failure
Reason: Account locked out
User Name: %1
Domain: %2
Logon Type: %3
Logon Process: %4
Authentication Package: %5
Workstation Name: %6
Windows Server 2003 adds these fields:
Caller User Name:-
Caller Domain:-
Caller Logon ID:-
Caller Process ID:-
Transited Services:-
Source Network Address:10.42.42.180
Source Port:0
Top 10 Windows Security Events to Monitor
Free Tool for Windows Event Collection