 Windows Security Log Event ID 4826
Windows Security Log Event ID 4826

4826: Boot Configuration Data loaded
On this page
Windows logs this event at startup to document the current Boot Configuration Data settings with particular security relevance. BCD data is configured with bcdedit.exe.
These settings should not normally change and could indicate serious security breaches if they do. You may see HyperVisor launch type change if admin enables/disables HyperV.
You shouldn't normally see DisallowMmConfig, system event logging, kernel debugging, test signing, flight signing, disabled integrity checks, hypervisor debugging set to yes or any hypervisor load options.
If you are using DeviceGuard and/or CredentialGuard you don't want to see VSM turned off.
Free Security Log Resources by Randy
Subject
Always logged by SYSTEM and logon ID 0x3e7
General Settings:
- Load Options: Usually "-" but determined by bcdedit -set loadoptions such as DISABLE_INTEGRITY_CHECKS
- Advanced Options: Yes/No refers to the legacy F8 Advanced Options menu at boot time and whether it was pressed
- Configuration Access Policy: Default or DisallowMmConfig based on bcdedit -set CONFIGACESSPOLICY which controls whether Windows uses memory mapped I/O to access a PCI manufacturer's configuation space or falls back on the Hardware Abstraction Layer.
- System Event Logging: Yes/No based on bcdedit -event and controls if remote event logging is enabled. Logs can be sent out via serial, USB or to the network.
- Kernel Debugging: Yes/No based on bcdedit -debug
- VSM Launch Type: Off/Auto based on bcdedit /set vsmlaunchtype. Virtual Secure Mode (aka VBS) isolates lsass.exe in a Hyper-V container to protect against mimikatz style attacks.
Signature Settings:
- Test Signing: Yes/No based on bcdedit -set testsigning. Allows device drivers signed by any certificate to load
- Flight Signing: Yes/No based on bcdedit -set flightsigning. Required for Insider Preview builds.
- Disable Integrity Checks: Yes/No based on bcdedit -set nointegritychecks and allows unsigned drivers to load
HyperVisor Settings:
- HyperVisor Load Options: Usually "-" but based on bcdedit -set hypervisorloadoptions. Possible option is NOFORCESNOOP which specifies whether the hypervisor should enforce snoop control on system IOMMU.
- HyperVisor Launch Type: Off/Auto based on based on bcedit -set hypervisorlaunchtype and determines if Hyper-V is enabled or not.
- HyperVisor Debugging: Yes/No based on bcedit -set hypervisordebug
Supercharger Free Edition
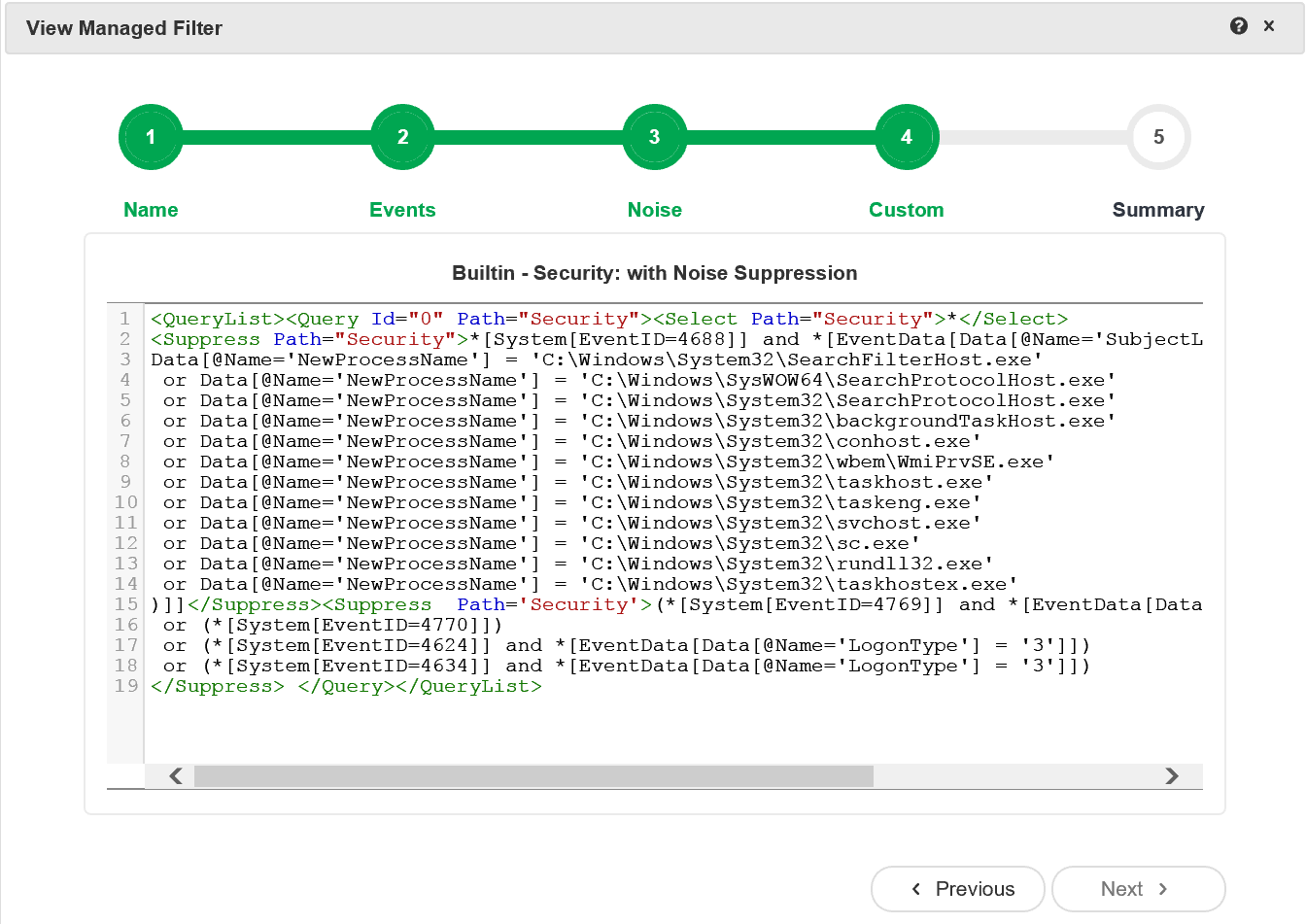
Supercharger's built-in Xpath filters leave the noise behind.
Free.
Boot Configuration Data loaded.
Subject:
Security ID: SYSTEM
Account Name: -
Account Domain: -
Logon ID: 0x3E7
General Settings:
Load Options: -
Advanced Options: No
Configuration Access Policy: Default
System Event Logging: No
Kernel Debugging: No
VSM Launch Type: Auto
Signature Settings:
Test Signing: No
Flight Signing: No
Disable Integrity Checks: No
HyperVisor Settings:
HyperVisor Load Options: -
HyperVisor Launch Type: Auto
HyperVisor Debugging: No
Top 10 Windows Security Events to Monitor
Free Tool for Windows Event Collection