 Windows Security Log Event ID 4615
Windows Security Log Event ID 4615

| Operating Systems |
Windows 2008 R2 and 7
Windows 2012 R2 and 8.1
Windows 2016 and 10
Windows Server 2019 and 2022
Windows Server 2025
|
Category
• Subcategory | System
• System Integrity |
|
Type
|
Success
|
Corresponding events
in Windows
2003
and before |
519
|
4615: Invalid use of LPC port
On this page
LPC is used for communication between threads or processes or for communication between kernel mode and user mode components. The communication can be on the same computer between the client and server functions. In 2000 there were several LPC port spoofing vulnerabilities patched for Windows NT.
I haven't been able to produce this event. Have you? If so, please start a discussion (see above) and post a sample along with any comments you may have! Don't forget to sanitize any private information.
Free Security Log Resources by Randy
Subject:
- Security ID: %1
- Account Name: %2
- Account Domain: %3
- Logon ID: %4
Process Information:
Other Information:
- Invalid Use: %5
- LPC Server Port Name: %6
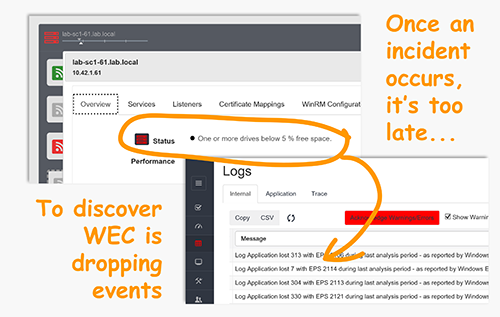
Supercharger Enterprise
Invalid use of LPC port.
Subject:
Security ID: %1
Account Name: %2
Account Domain: %3
Logon ID: %4
Process Information:
PID: %7
Name: %8
Other Information:
Invalid Use: %5
LPC Server Port Name: %6
Windows Local Security Authority (LSA) communicates with the Windows kernel using Local Procedure Call (LPC) ports. If you see this event, an application has inadvertently or intentionally accessed this port which is reserved exclusively for LSA's use. The application (process) should be investigated to ensure that it is not attempting to tamper with this communications channel.
Top 10 Windows Security Events to Monitor
Free Tool for Windows Event Collection