 SQL Server Audit Log Event ID 24145
SQL Server Audit Log Event ID 24145

24145: Issued an impersonate within database scope command (action_id IMP; class_type US)
This is an event from
SQL Server
audit event from
LOGbinder SQL
generated by
.
On this page
A command to switch the execution context of the session to the specified database user was issued
Free Security Log Resources by Randy
| Field |
Description |
| Occurred |
When event was reported by SQL Server |
| Authorization result |
If the command passed authorization checks |
| Session ID |
ID of the session on which the event occurred |
| User |
|
| Server |
|
| Database |
Database affected by the event |
| Original context |
|
| |
Server login |
Original context server login |
| |
Database user |
Original context database user |
| Target context |
|
| |
ID |
Target context ID |
| |
Database user |
Target context database user |
| Statement |
Transact-SQL statement |
Supercharger Free Edition
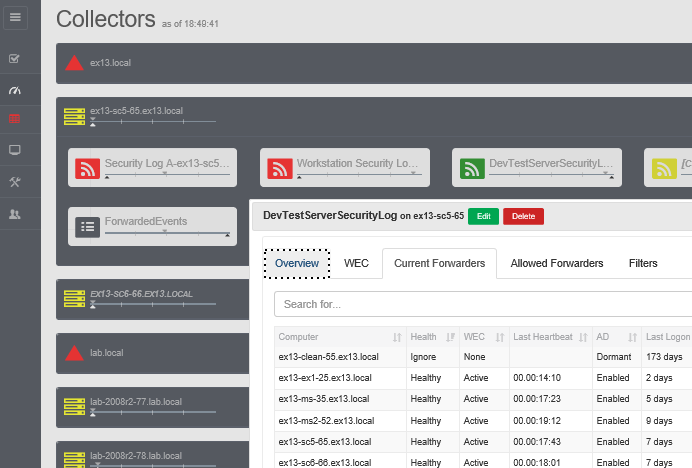
Your entire Windows Event Collection environment on a single pane of glass.
Free.
This Event Is Produced By

Which Integrates with Your SIEM
Issued an impersonate within database scope command
A command to switch the execution context of the session to the specified database user was issued
Action Group: DATABASE_PRINCIPAL_IMPERSONATION_GROUP
Occurred: 8/22/2013 6:07:52.0000000 PM
Authorization result: Access allowed
Session ID: 67
User: LB\Administrator
Server: DEV3
Database: TestDatabase
Original Context
Server login: LB\Administrator
Database user: dbo
Target Context
ID: 5
Database user: TestUser1
Statement: ALTER AUTHORIZATION ON XML SCHEMA COLLECTION::TestSchemaCollection TO TestUser1
For more information, see http://www.ultimatewindowssecurity.com/securitylog/encyclopedia/event.aspx?eventid=24145
Top 10 Windows Security Events to Monitor
Free Tool for Windows Event Collection